Introduction
Fast Reroute (FRR) is one of the defining capabilities of RSVP-TE, enabling networks to recover from failures in tens of milliseconds rather than waiting for full control-plane convergence. By precomputing backup paths and shifting protection into the data plane, FRR allows traffic to be redirected almost instantaneously at the point of failure (Point of Local Repair – PLR).
However, RSVP-TE does not implement FRR in just one way. It offers two foundational protection models—detour LSPs and facility backup—that take fundamentally different approaches to solving the same problem. More recently, enhancements such as constraint-aware bypass and emerging signaling extensions have begun to blur the line between these models, introducing a hybrid approach that balances scale with precision.
Understanding how these mechanisms differ—and where they converge—is critical when designing resilient, traffic-engineered networks.
Detour LSPs: Precision
Detour-based FRR, often referred to as one-to-one protection, takes a highly granular approach. For every primary LSP, each hop (PLR) along the path can establish its own dedicated backup LSP, known as a detour. These detours are signaled independently and are uniquely associated with their corresponding primary LSP.
This design allows each LSP to have a tailored backup path that reflects its specific constraints and requirements. When a failure occurs, the PLR simply switches traffic from the primary LSP onto its associated detour, ensuring a seamless continuation toward the destination.
The advantage of this approach lies in its precision. Because each LSP is protected individually, the network can optimize backup paths on a per-LSP basis, accommodating strict policies, bandwidth requirements, or various other path constraints. To limit network overhead, each detour does attempt to merge back into the LSP as soon as possible.

This precision comes at a cost. The number of detour LSPs grows linearly with network size, leading to increased control-plane activity and operational challenges. These factors may limit the practicality of detours in large-scale deployments.
Facility Backup: Efficiency Through Sharing
Facility backup, or many-to-one protection, takes a different approach by protecting network resources rather than individual LSPs. Instead of building per-LSP backups, the network establishes shared bypass tunnels that protect links (next-hop bypass LSPs) or nodes (next-next-hop bypass LSPs).
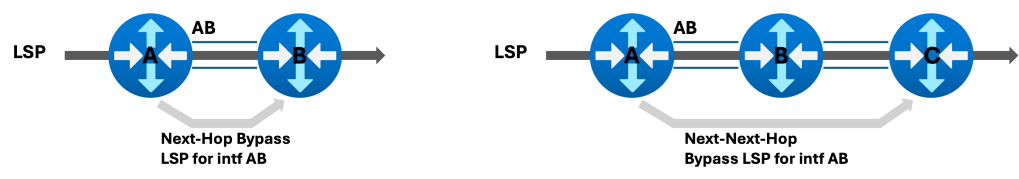
A single bypass LSP can carry traffic for multiple primary LSPs traversing the protected resource. When a failure occurs, the PLR redirects all affected traffic into this shared tunnel, which merges back into the original path downstream at a merge point (MP).
This model reduces RSVP state and signaling overhead, making it more scalable and operationally efficient. For large networks, this efficiency may be a deciding factor.
The trade-off is reduced granularity. Because multiple LSPs share the same bypass, the ability to optimize for individual constraints is limited, and bandwidth must be managed at an aggregate level.
Optimization and Constraint-Aware Bypass: Bridging Scale and Precision
Constraint-aware bypass represents an important evolution of facility backup, introducing a hybrid model that blends shared protection with greater sensitivity to LSP-specific requirements. Rather than computing bypass tunnels based solely on local PLR policy, this approach allows the backup path to better reflect constraints such as affinities, bandwidth, and other traffic engineering attributes of the LSPs requesting protection.
The result is a more informed form of facility protection. Multiple LSPs can still share a bypass tunnel, preserving scalability, but that tunnel is no longer entirely generic—it is better aligned with the characteristics of the traffic it protects. In practice, this reduces the mismatch between primary and backup behavior that can occur in traditional facility backup.
This concept is further extended by emerging RSVP-TE extensions that allow the headend to signal optimization intent to the PLR. These extensions enable the inheritance of objectives such as minimizing IGP cost, TE metric, delay, or available bandwidth along with bounded constraints that must be respected during backup path computation. This shifts FRR from a purely local repair mechanism toward a more coordinated model, where backup paths are influenced by end-to-end design goals.
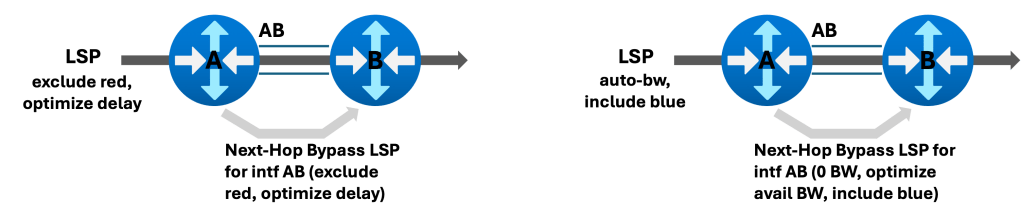
Constraint-aware bypass, combined with intent signaling, effectively creates a middle ground—retaining the efficiency of shared protection while reintroducing elements of per-LSP awareness traditionally associated with detours.
Behavior Under Failure
The differences between these approaches become most apparent during failure scenarios. With detour-based protection, each LSP is rerouted onto its own precomputed path, often resulting in diverse and highly optimized traffic flows even under failure conditions. This provides strong alignment with the original intent of each LSP but requires significant pre-established state.
Facility backup simplifies this behavior by redirecting all affected LSPs into a shared bypass tunnel. The switchover is straightforward and efficient, but it may temporarily concentrate traffic along a single alternate path, regardless of the individual characteristics of each LSP.
Constraint-aware bypass alters this dynamic. While traffic may still be funneled into shared tunnels, those tunnels are more likely to reflect the constraints and objectives of the protected LSPs. The result is a failure response that retains much of the simplicity of facility backup, but with behavior that more closely resembles the intent-driven outcomes of detour-based protection.
Choosing the Right Approach
Selecting the appropriate FRR model depends on the priorities and scale of the network.
Detours are best suited for environments where precision and strict adherence to per-LSP constraints are paramount. They provide unmatched control and deterministic behavior but are typically limited to smaller-scale or highly specialized deployments due to their overhead.
Facility backup remains the dominant choice for large networks, offering scalability, simplicity, and operational efficiency. For many operators, its behavior is sufficiently robust, even if it lacks fine-grained optimization.
Constraint-aware bypass introduces a compelling alternative. It is particularly well-suited for networks that require scalability but cannot fully compromise on path fidelity or constraint adherence. By blending shared protection with selective awareness, it offers a practical balance between the two traditional models.
Conclusion
Detour LSPs and facility backup were originally conceived as two distinct approaches to Fast Reroute, each optimizing for a different set of priorities. Detours emphasize precision and per-LSP control, while facility backup prioritizes scalability and efficiency.
Today, that distinction is becoming less rigid. Innovations such as constraint-aware bypass and optimization-aware signaling are introducing a hybrid model that combines the strengths of both approaches. These mechanisms allow networks to maintain the scalability of shared protection while better aligning backup behavior with the intent of the primary LSPs.
Ultimately, the goal of FRR is not just rapid recovery, but predictable recovery. As networks evolve, the ability to control not only how fast traffic is protected, but how intelligently it is rerouted, is becoming just as important as the speed of the switchover itself.
Leave a comment